How We Deliver Cybersecurity Services
Our cybersecurity services are tailored for small businesses that cannot afford to guess, wait, or gamble with their data. We deliver clear protection, proactive support, and tools that actually work.
01
Risk Management
We perform threat assessments and vulnerability scans to uncover weak spots across your systems. Then we provide practical, actionable steps to secure your infrastructure and reduce future risk exposure.
02
Layered Protection
We deploy layered defenses across devices, networks, and the cloud. With antivirus, MFA, email security, and endpoint monitoring, threats are stopped before reaching your business.
03
End-User Training
We train employees to spot phishing, social engineering, and risky actions. Ongoing education helps reduce errors and keep accounts and data protected.
04
Active Oversight
We monitor threats, respond to alerts, and stay ahead of attacks with continuous oversight. Our team keeps your tools updated, your policies current, and your environment protected as threats evolve.

Why You Might Need Cybersecurity Help
Small businesses are the top target for cyberattacks, yet many do not realize they are vulnerable until it is too late. Without layered protection and proper planning, one breach can shut you down fast.
Whether you are worried about phishing, compliance, or ransomware, you need a cybersecurity partner who helps you prevent problems, not just react to them. We give you visibility, strategy, and peace of mind.
Why Choose Protek-IT - Top Cybersecurity Company Chicago
We do not sell fear. We provide clear, proven cybersecurity services built around how your business actually operates. Our job is to prevent problems, reduce risk, and give you the confidence to move forward.
Protek-IT protects Chicago’s small businesses and nonprofits with layered security, employee training, and daily monitoring. You get real protection without unnecessary tools, bloated software, or scare tactics that distract from what matters.
Our cybersecurity services defend your business against the most common and damaging threats. We provide managed antivirus, threat monitoring, phishing training, Microsoft Defender setup, and full support to reduce your risk.
We protect your users, secure your data, and build a defense strategy that matches how your team actually works. Everything is tailored, tested, and supported so your business can move forward safely.
We scan your systems to identify threats and misconfigurations. Once we understand where the risk is, we provide recommendations and apply changes to secure your devices, users, and network.
You get a clear view of your security status, not a confusing report. Our remediation steps are easy to understand and built around your infrastructure.
Human error is the cause of most security breaches. We help train your staff to recognize phishing attempts, protect credentials, and report suspicious behavior before damage is done.
Our training program includes regular refreshers and phishing simulations so you know where help is needed.
If your team uses Microsoft 365, you already have access to powerful security tools. We help you configure and manage Defender for Business, MFA, and cloud security features properly.
You get protection without needing to buy third-party tools.
Cybersecurity is not a one-time project. We provide ongoing support, monitoring, and updates so your protection improves continuously and adapts to new threats as they emerge.
If you need help with an alert or incident, we respond fast and resolve the issue directly.
Trusted Cybersecurity Services For Chicago Teams
Our cybersecurity services are built around visibility, protection, and prevention. Businesses rely on us because we take security seriously and deliver support that addresses real risks, not theoretical ones or generic checklists.
The Protek IT Team
We make IT work for YOU

Greg Barsky
I am originally from Bulgaria and moved to the United States in 1996. Here, I've lived in New York, Pennsylvania and California.
I moved to Georgia in 1999. I love the south, the heath, the humidity, the trees, the sound of cicadas in the summer. I've been working in IT my whole life, and specialize in remote management and monitoring.
In my free time I try to keep my 4 year old son out of trouble, I also like working on DIY projects around the house.

Andrew Flechtner
I was born and raised in Pittsburgh before moving to Chicago 12 years ago.
If I'm not out bicycling, I like to watch hockey (go Penguins!), dive deep into the New York Times crossword puzzle archive, or play tennis with my wife.

Matt Jarvis
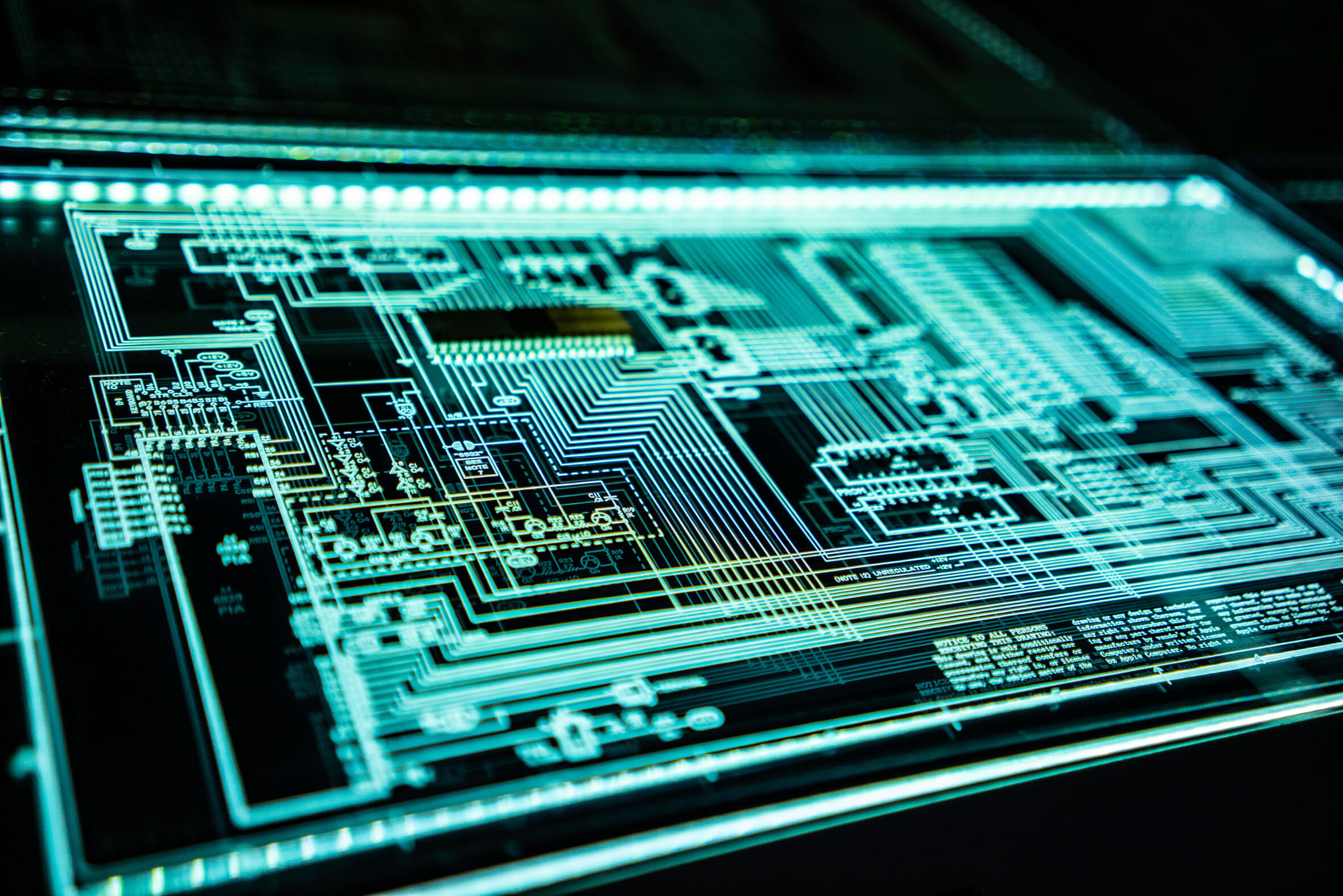
A native Chicagoan, I became interested in computers when we got our Apple IIe. I started my own computer consulting company in 2002 and acquired my first employees in 2005. I sold Blu Lin IT to Protek-IT in 2023 and am happy to be a part of the team!
My lovely family, travel, and beach volleyball are my passions outside of work.
FAQs
Get Help That Actually Helps
Straight Answers No Surprises
Talk to a team that fixes problems, not one that creates more. Book a free consultation to see how our IT services actually make life easier for your business.






















